There are some who consider Decker to be a true roguelike, but I found it played so differently to traditional roguelikes that I hesitate to call it one, exactly. But it certainly draws inspiration from roguelikes, and the end result is quite interesting.
You see, Decker is a game about hacking. Not hacking and slashing, as most roguelikes are, but hacking as in breaking into computer systems and stealing files. Drawing heavy inspiration from William Gibson’s Neuromancer, it casts the player as the titular Decker, a 22nd century hacker who is contracted to cruise through the virtual reality of the Matrix and steal valuable data. It lets you lead a dangerous but alluring life of corporate espionage and high-tech gadgetry. Well, eventually. In the beginning you are living in poverty, have a bare-bones cyberdeck (read: futuristic computer used for hacking purposes), and can only get a job breaking into the local Radioshack computer system to reset someone’s sick days, or something. A smart Decker doesn’t ask for the details. As you gain cash and a reputation, however, more meaty jobs start to appear, and you can upgrade your hardware and software to tackle some higher-security systems. This is the first and most obvious way that Decker differs from traditional roguelikes: rather than exploring a single dungeon or world, the player will tackle many different procedurally-generated computer systems, connected by an overarching time management game that lets one divide time between writing new programs, resting to recover from injury (yes, you can be physically injured when you’re jacked into cyberspace), or completing contracts in order to make rent at the end of the month.
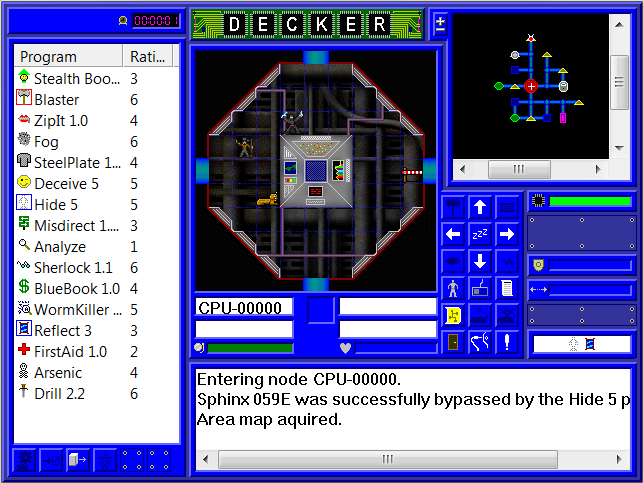
This time management stuff is controlled with some simple menus. These menus, like the rest of the game, have very basic graphics, to the point that some players might be turned off by the game’s look. It is possible to install alternate skins, but don’t expect too much from the visuals; it is inspired by the roguelike ethos of substance over style, after all. While most of the menus are easy to understand, the sections about the different software and hardware components can be confusing at first. Fortunately, there’s a full manual included with the game to explain it all. Unfortunately, this manual is written in the form of a Microsoft Help File, a format that is no longer supported in Windows Vista or Windows 7. This can be fixed through a quick download from Microsoft, and you’re going to want to fix it; if you thought the deck components were confusing, then you’re really going to be in trouble when you try to tackle your first hacking job. I figured hacking a system would be similar to exploring a dungeon in a traditional roguelike. I was very wrong.
First, there’s the way you move. In a traditional roguelike, a player explores the dungeon one tile at a time, moving around rooms and corridors. In Decker, the computer systems are presented as a network of nodes, and within each node, there is no movement at all. Movement occurs between nodes only, akin to exploring a traditional roguelike room by room rather than tile by tile. While the display shows the player, enemy ICE (Intrusion Countermeasure Electronics, i.e. software that is trying to kill the player), and other interesting features of the current node, the placement of these is largely meaningless. Everything in a given node is simply there. ICE can attack you, and you it, as long as you are in the same node; there’s no need to position yourself alongside the enemy first. Although if you are attacking the ICE, you’re probably doing something very, very wrong.
That’s the second big difference between Decker and most roguelikes: Decker is a stealth game. Sure, some roguelikes let the player choose a stealthy character, but in Decker stealth is pretty much the only viable option. Most of the time, you will be hiding from ICE, deceiving ICE with false passcodes, or running away and trying to shake pursuers if you are detected. This is all done with programs, akin to the various equipment that one would use in a traditional roguelike. Attack and Defense programs are used for combat, but the stealthy programs are far more important. Hide programs help keep you undetected as you move through the system, and Deceive programs will trick ICE into passing you by if they see you and ask for a passcode. If you’re caught, you’ll want a Silence program to “hush” the current node so the ICE doesn’t raise an alarm, and then you can either fight or run. If you’re running, judicious use of a Smoke program will prevent the enemy ICE from following you as you leave the node. There are plenty more programs too, including a stealthy virus attack that can take out ICE without turning it hostile (useful when you need to get rid of a node guardian in order to access some important processes), boost programs that temporarily raise attack or stealth values before attempting a particularly tricky task, and programs that can scan for valuable files to steal. The various nodes in a system also have unique functions. I/O nodes control some real-world thing, like fire alarms, and a contract will often ask you to activate or deactivate these. Data store nodes contain files ripe for stealing, often guarded by special encryption ICE. And the almighty CPU node lets you grab a map of the system or even crash it completely, if you can get past its powerful guardian ICE.
Successfully completing contracts not only earns you some much-needed cash but also grants skill points that let you raise your proficiency in general things like stealth, defense, programming and chip design. You can spend your cash on new hardware or software, but the best stuff you’re going to have to make yourself, which means not only bumping up your skill in the relevant areas but also delegating time towards writing new programs and designing new chips — time you could be spending completing more contracts. Once you’ve made enough money, you can upgrade your lifestyle, which increases the rent you have to play each month but also lets you increase your reputation and net some better-paying (and more dangerous) jobs.
Unfortunately, all of this quickly becomes a rather repetitive game of numbers. You complete contracts to increase your skills, which let you get some better equipment, which lets you tackle tougher jobs, so you can bump your skills some more. While the more difficult computer systems become larger and more dangerous to navigate, the actual obstacles don’t change much; enemy ICE simply comes at higher levels, which means you need higher level versions of your Hide and Deceive programs to sneak past it, and better Attack and Defense programs to fight it. Once you have these, you can tackle tougher jobs with better ICE, and so on and so on. There isn’t even an end goal, besides upgrading to the most opulent lifestyle and gaining the highest possible reputation. It’s a bit of a shame, but I don’t want to be too hard on Decker because it’s essentially an unfinished, abandoned project. I’d love to see a game take some of these design concepts and make something a little more meaty out of them. Greater variety in the enemy ICE at higher levels would go a long way, so players need to improve their strategies as well as their stats. Some sort of overarching plotline could be included to create more incentive to continue on to the end. And just generally adding more stuff would be cool — more node types, more ICE types, more mission objectives, more ways to get around obstacles. Currently, a player will simply want to pump all stats, programs and deck components as high as possible (with a possible emphasis on stealth before the rest), but with some redesigning it might be possible to create more specialized characters akin to classes in a traditional roguelike. Even within the general umbrella of “stealth”, I can imagine different ways to approach the game; for instance one character might focus on remaining completely invisible, deceiving programs and getting to the objective without anyone ever knowing they were there, while another character might take a more combat-focused approach, eliminating ICE and systematically dismantling the security before moving in.
Decker’s creator, Shawn Overcash, has made the source code for the game available via Sourceforge, so anyone inspired to make something more complex out of it is free to do so. In the meantime, the current version of Decker is free [EDIT: link no longer works, better get it from SourceForge instead], and it’s certainly worth checking out. It may not hold your interest for long, but there are some great ideas in there. Cyberspace awaits!



Leave a Reply